Red Piranha
Annual Threat Intelligence Report 2026
The threat landscape shifted in 2025.
Across 2025, Red Piranha analysed 80+ million security events, investigated 110 Advanced Persistent Threat (APT) campaigns, and tracked 7,800+ ransomware intrusions across government, defence, critical infrastructure, and enterprise environments.
This report distils operational intelligence from real monitored environments - not theoretical models into strategic guidance for enterprise security leaders.
SECURITY EVENTS ANALYSED
APT CAMPAIGNS INVESTIGATED
RANSOMWARE INTRUSIONS TRACKED
RANSOMWARE VOLUME INCREASE YOY
FIVE DEFINING FINDINGS
Five findings that change 2026 planning
Espionage-first intrusions overtake ransomware-first attacks
Attackers optimise for durable access and identity control before impact.
1
EDR bypass is now baseline tradecraft
Layered evasion techniques degrade endpoint visibility long before payload execution.
2
Identity is the primary choke point
Token theft, session reuse, and privilege escalation are dominant patterns.
3
Ransomware groups operate as structured enterprises
Access brokers, affiliates, and negotiation teams drive scale and precision.
4
Nation-state and hybrid actors dominate the threat landscape
China-aligned activity accounted for over 40% of observed APT campaigns.
5
THE DEFINING SHIFT
Access is the product.
Impact is optional.
'Time to encryption' is no longer a reliable indicator of intrusion success or failure.
The attacker may already have what they came for long before ransomware is deployed.
Recovery without forensics can be a strategic failure: you may restore services while leaving persistence intact - and losing the evidence trail entirely.
“Assume endpoint visibility will be degraded, assume identity will be abused, assume cloud and SaaS will be used as attack infrastructure, and design for independent detection planes that still work when one layer is blinded.”
THE IDENTITY-CENTRIC INTRUSION MODEL - 2025
Initial Access
Identity Abuse
Discovery
Lateral Movement
EDR Degradation
Persistence
Objective
RANSOMWARE INTELLIGENCE
Volume rose,
precision increased.
7,800+
Ransomware records in 2025 (vs 4,643 in 2024)
Red Piranha observed that ransomware deployment increasingly followed access-establishment, reconnaissance, and control impairment phases - not the other way around. Manufacturing led sector exposure (~1,380 incidents), followed by Business Services (~1,250).
TOP ACTORS BY BREACH VOLUME
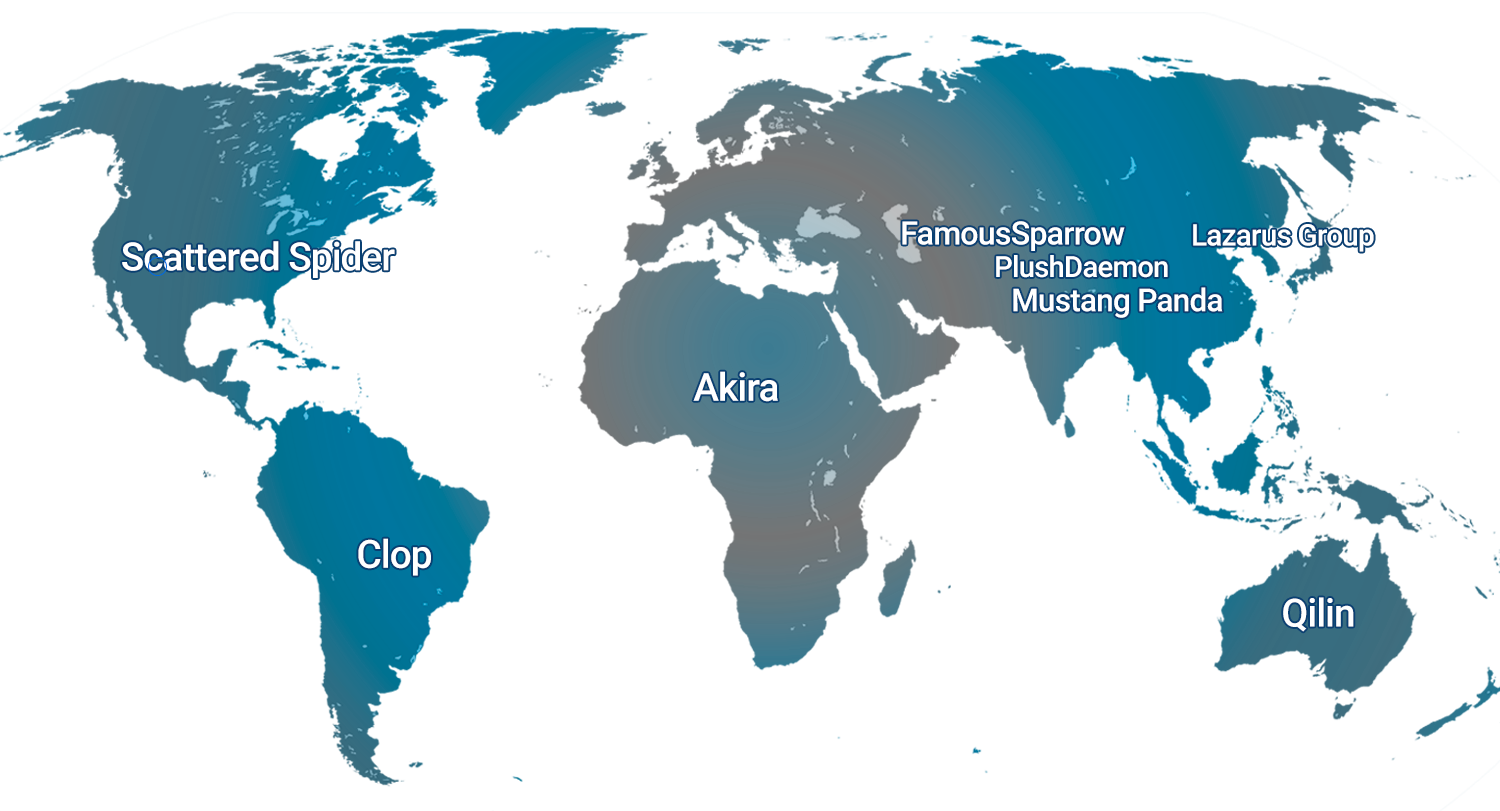
Qilin - 920
Akira - 610
Clop - 520
INCIDENTS PER MILLION (2025)
US - 13.2
AU - 12.1
CA - 12.0
NATION-STATE & APT
The rise of Nation-State
and APT campaigns.
The most damaging campaigns look like IT work until the moment they don't. 2025 APT tradecraft prioritises stealth, legitimacy mimicry, and long-duration operational persistence.
CHINA ALIGNED ACTIVITY
Approximately 50 distinct operations assessed as likely China-linked, representing over 40% of all observed APT campaigns. Government (35 incidents) and telecoms (14) are the most targeted sectors.
ESPIONAGE AS PRIMARY INTENT
Strategic access to decision-making systems, legal strategy, M&A data, and research pipelines. Financial/extortion motives account for 15.5%—including 'double-hat' operations used for funding or disruption cover.
EXECUTIVE ACTION PLAN
Your next 90-day
cyber priorities.
Within 30–90 days, executive leadership should be able to answer:
Can we detect identity-driven lateral movement without malware?
Can we investigate when EDR telemetry is incomplete?
Are Zero Trust controls enforced consistently across legacy, cloud, and OT?
Do we preserve forensic evidence before recovery?
Is external exposure treated as a continuous metric?
The report provides a pragmatic 30/90/180-day action framework.
ANNUAL THREAT INTELLIGENCE REPORT - 2026 EDITION
The threat model changed in 2025.
Has your defence?
Download the 2026 Annual Threat Intelligence Report
Plan for access, not just impact.
Understand how intrusions unfold before ransomware becomes visible and what resilient architecture looks like.