| New Threats Detection Added | • ClickFix |
| New Threat Protection | 113 |
| Newly Detected Threats | 17 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
ClickFix | ||||||||||||||||||
|
ClickFix is a social‑engineering–based vulnerability that exploits human trust rather than a flaw in software. It affects end users and their endpoints (e.g., Windows systems and browsers) by manipulating them into manually executing malicious commands. The general process involves a user being presented with a fake error, CAPTCHA, or security prompt that claims an issue needs to be “fixed.” When the user clicks the provided button, they are instructed to paste and run a command (often via PowerShell or a terminal), which then initiates the download and execution of malware on the system. This technique bypasses many technical security controls by relying on user interaction.
|
|||||||||||||||||||
|
Threat Protected:
|
04 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Exploit-kit | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 1 - April 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-1st-week-of-april-2026/652.
|
Vulnerability
|
CVSS
|
Description | Affected Version | Fixed Version | |
|
Fortinet FortiClient EMS (CVE-2026-35616)
|
9.1
|
Unauthenticated RCE - Fortinet FortiClient EMS contains an authentication bypass vulnerability that can allow an unauthenticated remote attacker to execute code on the device.
|
7.4.5 - 7.4.6
|
7.4.7
|
|
|
TrueConf Client (CVE-2026-3502)
|
7.8
|
Missing Integrity Check for Updates - TrueConf Client contains a vulnerability that can result in the installation of a malicious software update that's distributed via an on-prem TrueConf Server, the client trusts the update package from the server without any integrity checks to ensure it's a legitimate update. If an attacker is able to replace the update package on the TrueConf Server, all clients will be prompted to install this update resulting in the execution of malicious code.
|
<= 7.5.2
|
7.5.3
|
|
|
Google Dawn (CVE-2026-5281)
|
8.8
|
Remote Code Execution - Google Dawn contains a use-after-free vulnerability that could allow an unauthenticated remote attacker to execute code on the system upon visiting a specially crafted HTML page. This vulnerability may affect multiple Chromium-based products including Google Chrome, Microsoft Edge and Opera.
|
< 146.0.7680.178
|
146.0.7680.178
|
|
|
Citrix NetScaler (CVE-2026-3055)
|
9.3
|
Unauthenticated Memory Overread - Citrix NetScaler ADC and NetScaler Gateway contain a memory overread vulnerability that can allow an unauthenticated remote attacker to read memory from the appliance. The information contained within the leaked memory may contain credentials and session information which could lead to a further compromise of the device.
|
13.1 - 13.1-59.22
14.1 - 14.1-47.48
|
13.1-62.23
14.1-60.58
|
Updated Malware Signature (Week 1 - April 2026)
|
Threat
|
Description | |
|
Crpx0
|
CrpX0 is a malware loader and initial access tool commonly associated with phishing and social‑engineering campaigns. It primarily affects Windows endpoints, where it is used to establish an initial foothold on a system before deploying additional malicious payloads such as information stealers or remote access trojans. The general execution process involves tricking a user into downloading or running a malicious file or command (often delivered via phishing emails, fake downloads, or ClickFix‑style lures). Once executed, CrpX0 performs system reconnaissance, evades basic security controls, and retrieves further malware from attacker‑controlled infrastructure.
|
Ransomware Report |
|
|
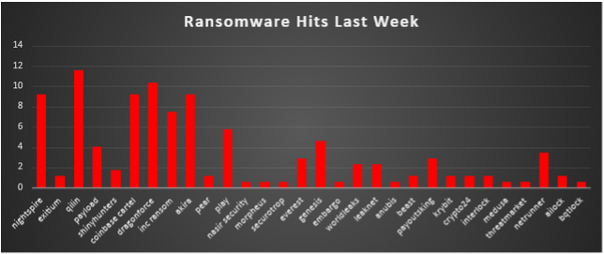
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity this week shows a fairly distributed threat landscape, with Qilin (11.56%) leading the pack, closely followed by DragonForce (10.4%). Not far behind, NightSpire, Coinbase Cartel, and Akira each account for 9.25% of total reported victims, indicating multiple dominant groups operating at scale rather than a single actor monopolizing attacks. INC Ransom (7.51%) and Play (5.78%) continue to maintain steady pressure, while mid-tier actors like Payload (4.05%), Genesis (4.62%), and Netrunner (3.47%) contribute to a notable share of activity. Lower frequency but still active groups include Everest (2.89%), PayoutsKing (2.89%), WorldLeaks (2.31%), and LeakNet (2.31%), suggesting a long tail of operators sustaining the ransomware ecosystem. Several smaller groups such as Exitium, Pear, Beast, Krybit, Crypto24, Interlock, and AILock (each ~1.16%), along with single-incident actors like Nasir Security, Morpheus, Securotrop, Embargo, Anubis, Medusa, ThreatMarket, and BQTLock (each ~0.58%), highlight the continued fragmentation and low barrier to entry in ransomware operations. Overall, the data reinforces that ransomware remains highly decentralised, with both established gangs and emerging players actively contributing to global attack volumes. |
NightSpire Ransomware
2.1 Threat Actor Description
Group Profile
NightSpire is a financially motivated ransomware group that first appeared in February 2025. The group is assessed with high confidence to be a rebrand of the earlier Rbfs ransomware operation, evidenced by: overlapping victims on both leak sites; shared operators (xdragon128 and cuteliyuan on BreachForums 2); and the cessation of all Rbfs activity coinciding precisely with NightSpire's launch.
Initially focused on data-theft-only extortion, NightSpire adopted a full double-extortion model within weeks of launching its dark web leak site on 12 March 2025 - combining file encryption with data exfiltration and public leak threats.
2.2 Tactics, Techniques & Procedures (TTPs)
Initial Access
FortiOS Exploitation (CVE-2024-55591): Primary access vector. NightSpire exploits the critical authentication bypass in FortiOS/FortiProxy Node.js WebSocket module, gaining super-admin privileges on FortiGate devices without valid credentials. Fortinet disclosed on 14 Jan 2025 (advisory FG-IR-24-535); exploitation by multiple actors observed since November 2024.
RDP Brute-Force & Credential Stuffing: Exposed RDP services targeted with stolen credentials sourced from dark web markets or prior infostealer campaigns.
Phishing Campaigns: Malicious attachments and drive-by downloads disguised as browser or security updates.
Additional Vectors: Exploitation of vulnerable VPN appliances; MFA fatigue attacks combined with VPN credential brute-forcing; RMM platform abuse through compromised MSPs.
Execution & Lateral Movement
Post-exploitation follows a structured three-phase attack chain using living-off-the-land binaries (LOLBins) to blend with normal administrative activity. All tools confirmed are observed in NightSpire intrusions.
- PowerShell - command execution and file enumeration across the network
- PsExec (PSEXESVC.exe) - remote process deployment across multiple hosts simultaneously
- WMI - lateral movement from a single source to multiple endpoints
- Mimikatz - credential harvesting: passwords, hashes, and Kerberos tickets from LSASS memory
- Everything.exe - rapid file and directory enumeration
- AnyDesk - persistent remote access channel
- Persistence via scheduled tasks and Registry Run keys
Data Exfiltration
Pre-encryption data theft follows a three-step workflow:
- Everything.exe execution for file discovery,
- 7-Zip archive creation with encrypted compression,
- Ooutbound transfer via WinSCP, MEGAcmd, or Rclone to attacker-controlled infrastructure. Exfiltration volumes range from tens of GB to hundreds of GB per victim.
Defence Evasion
- RC4/XOR/AES obfuscation layers in the Go-based payload to defeat static analysis
- Extended sleep intervals between encryption operations to avoid real-time behavioural detection
- Selective indicator removal and log manipulation post-execution
- Temporary file cleanup after payload execution
- OneDrive encryption without extension changes - files appear normal but fail to open, delaying detection
Impact
- Hybrid AES/RSA encryption: block encryption (1 MB chunks) for large files, full encryption for all others
- Each file receives unique AES key protected by attacker's RSA public key appended to file
- .nspire extension applied; readme.txt ransom note dropped in affected directories
- Parallel encryption of local systems and OneDrive cloud storage
- Countdown timers on DLS (48 hours - 90 days); direct emails to victim employees; publication of negotiation transcripts for non-payers
2.3 MITRE ATT&CK Mapping
|
Tactic
|
Technique ID
|
Description
|
|
Initial Access
|
T1190
|
Exploit Public-Facing Application - CVE-2024-55591 FortiOS
|
|
Initial Access
|
T1078
|
Valid Accounts - Stolen RDP/VPN credentials
|
|
Initial Access
|
T1566
|
Phishing - Malicious attachments/drive-by
|
|
Execution
|
T1059.001
|
PowerShell - Command execution & enumeration
|
|
Execution
|
T1047
|
WMI - Remote execution for lateral movement
|
|
Persistence
|
T1547.001
|
Registry Run Keys/Startup Folder
|
|
Persistence
|
T1053.005
|
Scheduled Task/Job
|
|
Priv. Escalation
|
T1003
|
OS Credential Dumping - Mimikatz/LSASS
|
|
Defence Evasion
|
T1027
|
Obfuscated Files - RC4/XOR/AES in Go binary
|
|
Defence Evasion
|
T1070
|
Indicator Removal - Log manipulation, temp cleanup
|
|
Defence Evasion
|
T1497
|
Virtualization/Sandbox Evasion - Sleep intervals
|
|
Credential Access
|
T1003.001
|
LSASS Memory Dumping - Mimikatz
|
|
Discovery
|
T1083
|
File and Directory Discovery - Everything.exe
|
|
Discovery
|
T1135
|
Network Share Discovery
|
|
Discovery
|
T1082
|
System Information Discovery
|
|
Lateral Movement
|
T1021.002
|
SMB/Windows Admin Shares - PsExec
|
|
Lateral Movement
|
T1219
|
Remote Access Software - AnyDesk
|
|
Collection
|
T1560
|
Archive Collected Data - 7-Zip
|
|
Collection
|
T1005
|
Data from Local System
|
|
Exfiltration
|
T1567
|
Exfiltration Over Web Service - MEGACmd/Rclone
|
|
Exfiltration
|
T1048
|
Exfiltration Over Alternative Protocol - WinSCP
|
|
C2
|
T1573
|
Encrypted Channel - TLS/Tor
|
|
Impact
|
T1486
|
Data Encrypted for Impact - AES/RSA (.nspire)
|
|
Impact
|
T1657
|
Financial Theft - Ransom demands $150K-$2M
|
2.4 Indicators of Compromise (IOCs) - NightSpire
Malware File Hashes
|
Type
|
Hash Value
|
|
SHA-1
|
989daab910436b48f422fe60daa17a95a486e87d
|
|
MD5
|
e2d7d65a347b3638f81939192294eb13
|
|
SHA-1
|
96bc46719eb773b1f13b63606898d1837cbd4169
|
|
MD5
|
82afcebc49f49b758de83b3275c91137
|
Threat Actor Communication Channels
|
Platform
|
Identifier
|
|
OnionMail
|
nightspireteam.receiver[@]onionmail[.]org
|
|
OnionMail
|
nightspire[@]onionmail[.]org
|
|
ProtonMail
|
nightspire[@]protonmail[.]com
|
|
Gmail
|
nightspire.support[@]gmail[.]com
|
|
qTox
|
3B61CFD6E12D789A439816E1DE08CFDA58D76EB0B26585AA34CDA617C41D5943CDD15DB0B7E6
|
|
Telegram
|
NightSpire-affiliated channels (multiple, rotating)
|
File & System Artifacts
|
Artifact Type
|
Value
|
Status
|
|
Ransom Note
|
readme.txt / nightspire_readme.txt / readme_2.txt
|
CONFIRMED
|
|
File Extension
|
.nspire (local); unchanged on OneDrive (stealth)
|
CONFIRMED
|
|
Binary Type
|
PE32+ executable (console) x86-64, Go-compiled
|
CONFIRMED
|
|
PsExec Service
|
PSEXESVC.exe across multiple hosts
|
CONFIRMED
|
|
Tools Observed
|
Everything.exe, Mimikatz, AnyDesk, 7-Zip, WinSCP, MEGACmd, Rclone
|
CONFIRMED
|
|
Operator Hostname
|
XDRAGON-SERVER1 (exposed on leak site) [Halcyon]
|
CONFIRMED
|
|
CVE Exploited
|
CVE-2024-55591 (FortiOS/FortiProxy auth bypass) [Fortinet FG-IR-24-535]
|
CONFIRMED
|
2.5 Detection & Mitigation - Crystal Eye 5.5
1. FortiOS Priority Patching & Perimeter Hardening
Immediately patch FortiOS to v7.0.17+ per Fortinet advisory FG-IR-24-535 for CVE-2024-55591. Audit all FortiGate devices for unauthorised admin accounts and unexplained configuration changes. Enforce MFA on all VPN/RDP access. Deploy CE WAF profiles to detect auth bypass and API abuse. Use CE IDPS Security ruleset in Detection & Protection mode on perimeter zones. Block legacy protocols. Escalate triggered IDPS alerts to CESOC.
2. Privilege Management & Credential Protection
Rotate admin/MSP credentials immediately. Disable unused accounts. Enforce least privilege for all service accounts. Enable ForceField brute-force protection to auto-block IPs exceeding failed login thresholds on RDP/VPN. Monitor Mimikatz/LSASS access indicators through CE XDR Endpoint sensors. Ingest Windows Security + Sysmon logs into CE SIEM for credential dumping detection. Deploy LSASS protection (PPL) on domain controllers.
3. Execution Control & LOLBin Detection
Use CEASR (CE Attack Surface Reduction) to block unknown Go binaries executing from %TEMP% / %APPDATA%. Restrict PsExec/WMI remoting to authorised admin workstations only. Create SIEM correlation rules for NightSpire kill-chain patterns: Everything.exe + 7-Zip + outbound WinSCP/MEGACmd/Rclone sequence. Alert on AnyDesk installations not sanctioned by IT. Monitor .nspire file creation and readme.txt drops via endpoint telemetry.
4. Network Controls & Segmentation
Ingest all NightSpire IOCs (hashes, email addresses, qTox ID) into CE AAI threat intelligence feeds and custom blocklists. Block outbound connections to MEGA cloud storage, known Tor exit nodes, and C2 infrastructure. Restrict SMB/WinRM east-west movement between network zones using CE Firewall Traffic Rules. Segment AD / file servers / backup infrastructure / critical systems from general user networks. Deploy inline IDPS profiles per security zone. Enable DNS.Insure sinkholing for known malicious domains.
5. Backup Hardening & Cloud Protection
Maintain offline/immutable backups following 3-2-1-1-0 strategy. Restrict backup server access - air-gap from production. NOTE: NightSpire does NOT delete Volume Shadow Copies - VSS recovery may be possible. Monitor OneDrive for unauthorized encryption activity (files inaccessible without extension change). Enable OneDrive version history with maximum retention. Configure CE DLP policies to detect anomalous large-volume outbound transfers. Trigger rapid SOAR actions: isolate hosts, block hashes/IOCs, rotate credentials, notify SOC. Validate restore procedures periodically.
Section 3 - Iran-US-Israel War IOCs
3.1 MuddyWater / MOIS - Active C2 Infrastructure
MuddyWater (aka Seedworm, TEMP.Zagros, Static Kitten, Mercury) is an Iranian Ministry of Intelligence and Security (MOIS)-affiliated APT group with a track record of targeting government, telecoms, and defence sectors across the Middle East, Europe, and North America. The C2 nodes below were identified via OTX AlienVault, ThreatHunter.ai, and ESET telemetry.
|
IP Address
|
Threat Actor
|
OTX Verdict
|
Top Tags
|
OTX Link
|
|
185.236.25.119
|
MuddyWater
|
Malicious
|
MuddyWater, Tsundere, MOIS
|
|
|
193.17.183.126
|
MuddyWater
|
Malicious
|
MuddyWater, Ethereum, Amazon-cert-spoof
|
|
|
194.11.246.101
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Hosterdaddy
|
|
|
194.11.246.78
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Fooder
|
|
|
209.74.87.100
|
MuddyWater
|
Malicious
|
MuddyWater, KeyC2, PersianC2
|
|
|
89.40.31.242
|
MuddyWater
|
Malicious
|
MuddyWater, Hosterdaddy, post-EpicFury
|
|
|
89.40.31.236
|
MuddyWater
|
Malicious
|
MuddyWater, ScreenConnect, RMM
|
|
|
212.232.22.136
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Hosterdaddy
|
|
|
62.106.66.112
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Hosterdaddy
|
|
|
157.20.182.49
|
MuddyWater
|
Malicious
|
MuddyWater, Sliver, C2
|
|
|
146.19.143.14
|
MuddyWater
|
Malicious
|
MuddyWater, C2
|
|
|
136.243.87.112
|
MuddyWater
|
Malicious
|
MuddyWater, C2
|
|
|
162.0.230.185
|
MuddyWater
|
Malicious
|
MuddyWater
|
|
|
104.237.233.40
|
MuddyWater
|
Malicious
|
MuddyWater
|
3.2 JaJoJoo LLC - Certificate-Spoofing Infrastructure
JaJoJoo LLC is a hosting entity (FranTech/BuyVM infrastructure) linked to Iranian APT certificate-spoofing operations. These IPs have been identified spoofing certificates from Apple, Microsoft, Yandex, DuckDuckGo, and GlobalSign to intercept traffic and facilitate man-in-the-middle attacks.
|
IP Address
|
Threat Actor
|
OTX Pulses
|
Top Tags
|
OTX Link
|
|
185.236.25.182
|
JaJoJoo LLC
|
4
|
JaJoJoo, Apple-cert-spoof, APT
|
|
|
185.121.15.29
|
JaJoJoo LLC
|
3
|
JaJoJoo, Yandex-cert-spoof, GlobalSign
|
|
|
185.121.15.127
|
JaJoJoo LLC
|
3
|
JaJoJoo, Microsoft-cert-spoof
|
|
|
185.236.25.233
|
JaJoJoo LLC
|
2
|
JaJoJoo, Microsoft-cert-spoof
|
|
|
193.17.183.89
|
JaJoJoo LLC
|
3
|
JaJoJoo, Microsoft-cert-spoof, MuddyWater
|
|
|
185.236.25.9
|
JaJoJoo LLC
|
2
|
JaJoJoo, DuckDuckGo-cert-spoof
|
3.3 MuddyWater - Active C2 & Infrastructure Domains
|
Domain
|
Threat Actor
|
OTX Link
|
|
worthscale.eu.com
|
MuddyWater
|
|
|
apro24docs.com
|
MuddyWater
|
|
|
aproenvoid.com
|
MuddyWater
|
|
|
countarctice.us
|
MuddyWater
|
|
|
vwafair.com
|
MuddyWater
|
|
|
processplanet.org
|
MuddyWater
|
|
|
magicallyday.com
|
MuddyWater
|
|
|
dokedge.de.com
|
MuddyWater
|
|
|
urbpart.us.com
|
MuddyWater
|
|
|
pushbeacon.org
|
MuddyWater
|
|
|
notifyblast.org
|
MuddyWater
|
|
|
iaresult.us.com
|
MuddyWater
|
|
|
vmbfat.eu.com
|
MuddyWater
|
|
|
pulpower.com
|
MuddyWater / Tsundere
|
|
|
1f2e18bbde8ecc30ee3307a4.net
|
MuddyWater / Tsundere
|
|
|
storetemu.shop
|
MuddyWater (phishing)
|
|
|
detainstitudent.online
|
Iran-aligned (phishing)
|
3.4 APT42 / Charming Kitten - Academic Phishing Cluster
APT42 (also known as Charming Kitten, TA453, Mint Sandstorm) is an IRGC-IS-affiliated group specialising in credential harvesting and targeted phishing against academics, journalists, and government officials. The following domains are assessed as part of an academic conference impersonation cluster. [Source: OTX AlienVault - verdict Suspicious pending further analyst confirmation]
|
Domain
|
Threat Actor
|
Verdict
|
OTX Link
|
|
researchsummitonline.com
|
APT42 / Charming Kitten
|
Suspicious
|
|
|
globalconference-hub.com
|
APT42 / Charming Kitten
|
Suspicious
|
3.5 Cotton Sandstorm / APT28 Overlap Domains
Cotton Sandstorm (aka Emennet Pasargad) is an Iranian-nexus group with confirmed overlapping infrastructure with Russian APT28 (Fancy Bear) in specific campaigns. The following domain was seized by the FBI:
|
Domain
|
Threat Actor
|
Verdict
|
Notes
|
OTX Link
|
|
vps-agent.net
|
Cotton Sandstorm / APT28 overlap
|
Malicious
|
FBI seized under warrant
|
3.6 Named OTX Pulses - Iran APT Cluster
|
Threat Actor
|
Pulse Title
|
Key IOCs
|
OTX Pulse Link
|
|
MuddyWater
|
MuddyWater Exposed - New C2 Infrastructure 2026
|
194.11.246.101, 209.74.87.100, worthscale.eu.com
|
|
|
MuddyWater
|
Iranian MOIS Cyber Operations - Post Operation Epic Fury
|
89.40.31.242, apro24docs.com, aproenvoid.com
|
|
|
MuddyWater
|
MuddyWater PowerShell C2 Beacons
|
194.11.246.78, 212.232.22.136, vwafair.com
|
|
|
JaJoJoo LLC
|
Iran APT Infrastructure - FranTech/BuyVM Hosting
|
185.236.25.119, 193.17.183.126, 185.121.12.143
|
|
|
MuddyWater/Tsundere
|
Tsundere Botnet Infrastructure - DinDoor Variant
|
193.24.123.68, pulpower.com, 1f2e18bbde8ecc30ee3307a4.net
|
|
|
MuddyWater/Tsundere
|
Iranian APT MuddyWater C2 Servers
|
193.24.123.68, 185.28.119.179, 62.60.226.179
|
|
|
MuddyWater
|
Blockchain-Based C2 Infrastructure
|
185.236.25.119, 193.17.183.126, ETH:0x2B77671c
|
|
|
MuddyWater
|
LevelBlue Labs - MuddyWater New C2 2026
|
194.11.246.101, 209.74.87.100, 212.232.22.136
|
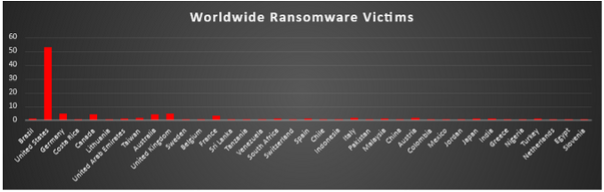
Ransomware Victims by Geography
This week’s ransomware activity highlights a heavily skewed global distribution, with the United States accounting for 52.6% of all reported victims - far exceeding the rest of the world combined and reinforcing its position as the primary target due to high financial returns and a large attack surface.
A second tier of consistently targeted nations includes Germany (4.62%), United Kingdom (4.62%), Canada (4.05%), and Australia (4.05%), reflecting a continued focus on developed economies with strong payout potential.
Mid-level activity is observed across countries such as France (3.47%), Italy (1.73%), Taiwan (1.73%), and Austria (1.73%), while regions including the United Arab Emirates, India, Japan, Turkey, and Malaysia (each ~1.16%) indicate ongoing expansion into emerging and Asia-Pacific markets.
The remaining countries, each contributing around 0.58%, form a long tail of opportunistic targeting, demonstrating that while ransomware operations are strategically concentrated in high-value regions, their execution remains globally distributed and indiscriminate.
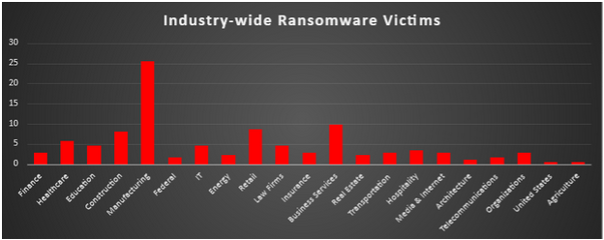
Industry-wide Ransomware Impact
This week’s industry-wise ransomware distribution clearly shows a strong concentration on high-revenue and operationally critical sectors, with Manufacturing leading at 25.43%, making it by far the most targeted industry due to its low tolerance for downtime and high likelihood of paying ransoms to resume operations quickly.
Business Services (9.83%), Retail (8.67%), and Construction (8.09%) follow as major targets, reflecting attackers’ focus on sectors with continuous operations and supply chain dependencies.
Mid-tier industries such as Healthcare (5.78%), Education (4.62%), IT (4.62%), and Law Firms (4.62%) remain consistently targeted due to the sensitivity of their data and urgency to recover systems. Smaller but still relevant activity is observed across Hospitality (3.47%), Finance (2.89%), Insurance (2.89%), Transportation (2.89%), Media & Internet (2.89%), and Organisations (2.89%), indicating a broad attack surface across service-driven sectors.
Meanwhile, lower-frequency targets like Energy (2.31%), Real Estate (2.31%), Federal (1.73%), Telecommunications (1.73%), and niche industries such as Architecture (1.16%), Agriculture (0.58%), and isolated entries highlight opportunistic attacks.
Overall, the pattern is clear—ransomware operators prioritise industries where downtime directly translates to financial loss, ensuring maximum leverage during extortion.