
| New Threats Detection Added | • MixShell • Nexcorium |
| New Threat Protection | 131 |
| Newly Detected Threats | 9 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
MixShell | ||||||||||||||||||
|
MixShell is a stealthy Windows based malware that is known to be distributed via infected ZIP archives in social engineering campaigns targeting supply-chain and manufacturing companies. It’s an in-memory implant that’s loaded via PowerShell and offers capabilities for file operations, reverse proxies, command execution and pipe-based interactive sessions. Exfiltration of data and command-and-control functionality uses encrypted DNS TXT record queries, with HTTP as a fallback.
|
|||||||||||||||||||
|
Threat Protected:
|
02 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Command-and-Control | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
|
Threat name:
|
Nexcorium | ||||||||||||||||||
|
Nexcorium is an Internet-of-Things (IoT) malware that is primarily used for DDoS attacks and is based on Mirai. It’s often spread by exploitation of known vulnerabilities and includes the capabilities to spread to other devices within the network by brute forcing default credentials. Upon infection, persistence is achieved using systemd and cronjobs with command-and-control communications to a hardcoded C2 server.
|
|||||||||||||||||||
|
Threat Protected:
|
01 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Trojan-Activity | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 1 - May 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-1st-week-of-may-2026/658.
|
Vulnerability
|
CVSS
|
Description | Affected Version | Fixed Version | |
|
7.8
|
Privilege Escalation - Linux Kernel contains a privilege escalation vulnerability that can allow an attacker to escalate their privileges to root. This vulnerability, dubbed 'Copy Fail', affects all mainstream Linux distributions with kernels built from 2017.
|
Check vendor advisories for affected products and versions.
|
|||
|
9.8
|
Authentication Bypass - WebPros cPanel & WHM (WebHost Manager), WP2 (WordPress Squared) contains an authentication bypass that can allow an unauthenticated remote attacker to gain access to the system. This vulnerability affects all versions of cPanel since version 11.40 (released 2013), successful exploitation can result in an attacker gaining root level access to the system.
|
Check vendor advisory for affected products and versions.
|
|||
|
8.4
|
Path Traversal - ConnectWise ScreenConnect contains a path traversal vulnerability that can allow an attacker to execute code on the system by uploading a specially crafted zip archive. This vulnerability is often used alongside an authentication bypass vulnerability (CVE-2024-1709) in exploitation from an unauthenticated standpoint, resulting in the execution of code in the context of the SYSTEM.
|
<= 23.9.7
|
23.9.8
|
||
|
4.3
|
Network Spoofing - Microsoft Windows Shell contains a vulnerability that can allow an unauthenticated attacker to perform spoofing over a network. Exploitation of this vulnerability occurs via auto-parsed LNK files and can result in the disclosure of Net-NTLMv2 hashes to an attacker.
|
Check vendor advisory for affected products and versions.
|
|||
Updated Malware Signature (Week 1 - May 2026)
|
Threat
|
Description | |
|
ErrTraffic
|
ErrTraffic is a self-hosted cybercrime platform that is used to automate ClickFix campaigns. It functions as a Traffic Distribution Platform (TDS) that enables threat actors to deploy custom ClickFix lures dynamically to a victim based on the browser or operating system.
|
|
|
XWorm
|
A Remote Access Trojan (RAT) and malware loader that's commonly used in cyberattacks to give attackers full remote control over a victim's system. It's part of a growing trend of commercialised malware sold or rented on dark web forums, often under the guise of a “legitimate tool.”
|
Ransomware Report |
|
|
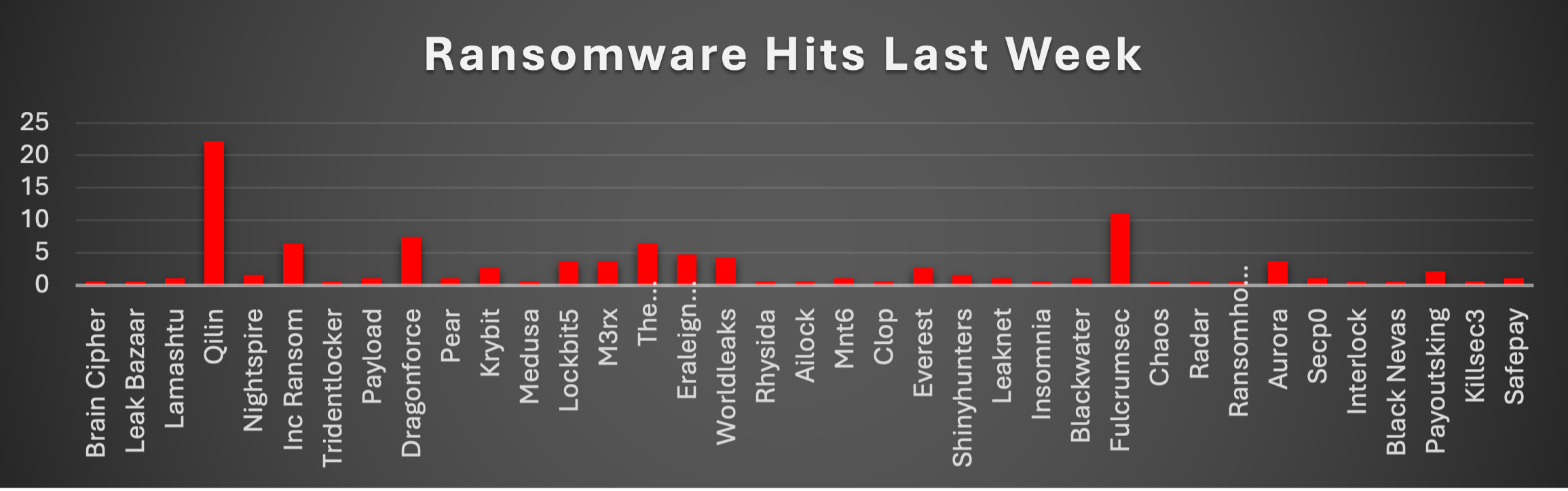
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity this week shows a clear dominance by a few high-impact groups, with Qilin leading aggressively (22.22%), making it the most active threat actor by a significant margin. This reflects strong operational scale and likely affiliate-driven campaigns. Fulcrumsec (11.11%) follows as the second most active group, indicating a notable surge in activity. Dragonforce (7.41%), along with Inc Ransom and The Gentlemen (6.35% each), also contributed heavily, reinforcing their continued presence in the threat landscape. Mid-tier actors such as Eraleign (APT73) (4.76%), Worldleaks (4.23%), and Lockbit5, M3rx, and Aurora (3.7% each) maintained steady operations, suggesting consistent but controlled campaign execution. Other groups including Krybit and Everest (2.65%), and Payoutsking (2.12%), showed moderate activity levels. Meanwhile, actors like Nightspire and Shinyhunters (1.59%), along with several others in the ~1% range (Lamashtu, Payload, Pear, Mnt6, Leaknet, Blackwater, Secp0, SafePay), indicate scattered but ongoing operations. A long tail of groups such as Brain Cipher, Leak Bazaar, Tridentlocker, Medusa, Rhysida, Ailock, Clop, Insomnia, Chaos, Radar, Ransomhouse, Interlock, Black Nevas, and Killsec3 (0.53% each) reported minimal activity, reflecting either niche targeting or early-stage campaigns. |
FulcrumSec Ransomware
Executive Summary
FulcrumSec (alias "The Threat Thespians") is a financially motivated, data-extortion-only criminal group active since September 2025. During the reporting window of 25 April - 01 May 2026, the group conducted its largest single leak-site dump to date - at least 21 new and re-published victims posted on 29 April 2026 - pushing its cumulative tracked victim count past 22 organisations.
The group does NOT deploy a traditional ransomware encryptor. Its model is "steal and squeeze" double-extortion against cloud-hosted data lakes (Azure, Databricks, AWS, MongoDB Atlas), with confirmed initial-access TTPs including CVE-2025-55182 (React2Shell, CVSS 10.0), abuse of unrotated credentials and API keys, and over-permissive AWS ECS task roles.
No public PE/ELF malware samples, hashes, or YARA rules exist on VirusTotal, MalwareBazaar, ThreatFox, ANY.RUN, or URLhaus tagged 'fulcrumsec.'
Threat Actor Overview
Identity, Origin and Structure
|
Attribute
|
Value
|
Verification
|
|
Primary moniker
|
FulcrumSec
|
Confirmed - vx-underground, WatchGuard, Dataminr, RansomLook, Shenouda
|
|
Alias
|
The Threat Thespians
|
Confirmed - WatchGuard, RansomLook, Dataminr
|
|
First observed
|
September 2025 (Avnet intrusion discovered 26 Sep 2025; public claim 7 Oct 2025)
|
Confirmed - Bleeping Computer, Dataminr, Shenouda
|
|
Actor type
|
Organised crime - pure data-extortion / data-broker
|
Confirmed - Shenouda, Dataminr, Group-IB
|
|
Motive
|
Financial - exclusive sale of stolen data to single buyer; double extortion
|
Confirmed
|
|
RaaS structure
|
None observed; no affiliate recruitment; no public encryptor
|
Confirmed - Shenouda Dec 2025 Update, Ransomware.live
|
|
Classification note
|
WatchGuard Ransomware Tracker lists FulcrumSec despite no encryption observed - possible occasional locker tooling or affiliate crossover
|
Unverified - tracker listing confirmed
|
|
Nation-state nexus
|
None alleged
|
Confirmed (no attribution)
|
|
Peer cluster
|
Warlock Group, Payouts King, RDAT Group (Arete Nov 2025); behavioural analogues: LAPSUS$, Karakurt, ShinyHunters
|
Confirmed
|
Targeted Sectors and Geographies
Sectors (per WatchGuard Ransomware Tracker and RansomLook 22-victim aggregate): Information Technology/SaaS, Banking & Finance, Healthcare & Medicine, Legal, Electronics & Robotics, Manufacturing, Mining & Quarrying, Fashion & Textiles, Media & Marketing, Charity & Nonprofits, Environmental Services, Automotive, Security & Cybersecurity.
Geographies: United States (~70% of victims), United Kingdom, Australia, India, Germany, Mexico, Colombia.
Targeted environments: Microsoft Azure storage accounts, Databricks notebooks/data lakes, AWS (ECS, Redshift, Secrets Manager, VPC databases), MongoDB Atlas clusters, Qualtrics, externally hosted cloud storage.
Malware Technical Analysis
CRITICAL CAVEAT:
No FulcrumSec malware sample exists. Searches of ANY.RUN, MalwareBazaar, ThreatFox, URLhaus, AlienVault OTX, and VirusTotal return no submissions tagged fulcrumsec. There are therefore no file hashes, encrypted file extensions, ransom-note filenames, mutex names, registry keys, or public YARA/Sigma rules.
What is confirmed is the group's toolset (living-off-the-land + cloud-native abuse):
|
Capability
|
Tool / Method
|
|
Initial cloud foothold
|
CVE-2025-55182 (React2Shell); unrotated cloud credentials and API keys (some dating to 2021)
|
|
Cloud enumeration
|
Stolen OpenAI API keys used to generate enumeration & exfiltration scripts (Avnet breach)
|
|
Data staging
|
Snappy-compressed Parquet partitions (1.1 TB → 7-12 TB raw at Avnet); .tar.gz archives
|
|
Data exfil channels
|
Direct cloud-to-cloud transfer; rclone-class tooling assessed likely
|
|
Negotiation channels
|
Email (Tutanota, self-hosted), Telegram, Tox, darkforums.st
|
|
Extortion infrastructure
|
fulcrumsec.net, data-removal.com + two Tor .onion mirrors
|
|
Reputational pressure
|
Counter-messaging: releases plaintext samples when victim downplays breach (Avnet, LexisNexis Lexis1234 incident)
|
Tactics, Techniques and Procedures
|
Tactic
|
TTP ID
|
Technique
|
FulcrumSec Implementation
|
|
Reconnaissance
|
T1593.003
|
Search Open Websites: Code Repositories
|
Mining Git history, CI/CD logs, S3/Blob misconfigs for exposed secrets
|
|
Resource Dev.
|
T1583.001
|
Acquire Infrastructure: Domains
|
Operates fulcrumsec.net, data-removal.com, two .onion services
|
|
Resource Dev.
|
T1586.003
|
Compromise Accounts: Cloud Accounts
|
Purchases credentials from IABs and infostealer-log markets
|
|
Initial Access
|
T1190
|
Exploit Public-Facing Application
|
CVE-2025-55182 (React2Shell, CVSS 10.0) - unauthenticated RCE in React Server Components Flight endpoint at LexisNexis
|
|
Initial Access
|
T1078.004
|
Valid Accounts: Cloud Accounts
|
youX: unrotated 2021-vintage credentials; no MFA on broker/admin accounts
|
|
Initial Access
|
T1566
|
Phishing
|
Inferred from LAPSUS$/Karakurt analogues
|
|
Execution
|
T1609
|
Container Admin Command
|
RCE within LawfirmsStoreECSTaskRole ECS task container; arbitrary commands under Node.js runtime
|
|
Execution
|
T1059
|
Command & Scripting Interpreter
|
Custom exfil scripts generated using victim's stolen OpenAI API keys (Avnet)
|
|
Persistence
|
T1078.004
|
Valid Accounts: Cloud Accounts
|
Retention of compromised IAM keys/API tokens until victim rotates all credentials
|
|
Privilege Esc.
|
T1548
|
Abuse Elevation Control
|
Single ECS task role granted read access to ALL AWS Secrets Manager entries - over-permissioned IAM escalation
|
|
Defence Evasion
|
T1550.001
|
Application Access Token
|
Direct API/session-token use bypasses MFA-protected interactive login
|
|
Defence Evasion
|
T1535
|
Unused/Unsupported Cloud Regions
|
Exfil staged entirely in cloud, evading EDR on endpoints
|
|
Credential Access
|
T1552.001
|
Unsecured Credentials: Files
|
53 plaintext AWS Secrets Manager entries harvested; weak Lexis1234 RDS master password
|
|
Credential Access
|
T1552.005
|
Cloud Instance Metadata API
|
IMDS hits (169.254.169.254) observed in CVE-2025-55182 campaign - inferred for FulcrumSec
|
|
Credential Access
|
T1555
|
Credentials from Password Stores
|
AWS Secrets Manager harvest including production Redshift master credentials
|
|
Discovery
|
T1526
|
Cloud Service Discovery
|
Enumeration of Redshift, VPC, ECS, Qualtrics, Databricks across victim cloud accounts
|
|
Discovery
|
T1580
|
Cloud Infrastructure Discovery
|
Mapped 17 VPC databases, 536 Redshift tables, 430+ VPC DB tables at LexisNexis
|
|
Discovery
|
T1619
|
Cloud Storage Object Discovery
|
Azure storage account & Databricks workspace enumeration at Avnet
|
|
Lateral Movement
|
T1550.001
|
Application Access Token (intra-cloud)
|
Cross-service movement via ECS task role permissions across AWS services
|
|
Collection
|
T1530
|
Data from Cloud Storage Object
|
2.04 GB Redshift+VPC data (LexisNexis); 300 GB MongoDB Atlas (youX); 1.1 TB compressed / 7-12 TB raw Parquet (Avnet)
|
|
Collection
|
T1213
|
Data from Information Repositories
|
Qualtrics survey platform, support-ticket systems, sales-tool databases
|
|
Collection
|
T1602
|
Data from Configuration Repository
|
VPC infrastructure maps, IAM policy dumps
|
|
C2
|
T1071.001
|
Application Layer Protocol: Web
|
HTTPS comms to attacker-controlled infra and Tor leak sites
|
|
C2
|
T1090.003
|
Multi-hop Proxy: Tor
|
Two .onion extortion/leak sites; Tor used for anonymous comms
|
|
Exfiltration
|
T1041
|
Exfiltration Over C2 Channel
|
Direct outbound from compromised cloud workload to actor-controlled cloud bucket
|
|
Exfiltration
|
T1567.002
|
Exfiltration to Cloud Storage
|
Stolen data retained in actor cloud storage; 'keys' handed to buyer
|
|
Exfiltration
|
T1020
|
Automated Exfiltration
|
Automated scripts generated using victim's own OpenAI API keys (Avnet)
|
|
Exfiltration
|
T1048
|
Exfiltration Over Alt. Protocol
|
rclone / FileZilla / cURL over HTTPS/SFTP - inferred from hunt guidance; not directly confirmed
|
|
Impact
|
T1657
|
Financial Theft (Extortion)
|
Demand for payment; 'steal-and-squeeze' model with leak-site double extortion
|
|
Impact
|
T1565.001
|
Stored Data Manipulation
|
Public release of internal emails, court summons, plaintext samples to refute victim downplaying
|
|
Impact
|
T1486
|
Data Encrypted for Impact
|
NOT OBSERVED - group does not encrypt endpoints or files
|
Indicators of Compromise
File-Hash IOCs
Non-AVAILABLE: FulcrumSec does not deploy a binary encryptor.
Network Infrastructure IOCs (All Confirmed)
|
Type
|
Value
|
Notes
|
|
Clearnet domain
|
fulcrumsec.net
|
Primary leak/extortion site; 100% uptime past 30 days
|
|
Clearnet domain
|
data-removal.com
|
Secondary extortion brand domain
|
|
Tor .onion
|
4e3p3in2bl67hxchuwza7qvnpe7pyeloyztr5fnh257fxkovfhappjyd.onion
|
Primary DLS - 100% uptime; /shame/ directory hosts named victims
|
|
Tor .onion
|
gsgot6tua7ffammwdv6vpxkog32b4z7qivtqkxz55afq2hkt2o24w5yd.onion
|
Secondary mirror - currently DOWN but retain on blocklists
|
|
Dark forum
|
darkforums.st
|
Primary auction venue for single-buyer data sale
|
Email & Messaging IOCs (All Confirmed)
|
Type
|
Value
|
|
Email
|
|
|
Email
|
|
|
Email
|
|
|
Telegram
|
@fulcrumsec (https://t.me/fulcrumsec)
|
|
Telegram
|
@threatspians (https://t.me/threatspians)
|
|
Tox ID
|
6A5E9ED3D7D26CAD5E6CA4E229CC80DA3C13AD002F73D4450078284E6C762F6DBDCF1FE9BF44
|
|
Tox ID
|
969F8BE40B09537CD2A5038B9DA4BADE71C5F35DD666CC0D7632A6812D7AF72626D422D22540
|
Vulnerabilities Exploited
|
CVE
|
Product
|
CVSS
|
Status
|
|
CVE-2025-55182
|
Meta React Server Components - Flight protocol unsafe deserialisation
|
10.0 (Critical)
|
Confirmed - CISA KEV 5 Dec 2025; LexisNexis primary entry vector
|
Behavioural/Hunt IOCs
|
Indicator
|
|
Inbound HTTPS POST containing next-action, rsc-action-id, $@, _response, or status:resolved_model patterns to React/Next.js endpoints
|
|
Outbound traffic from cloud workloads to IMDS 169.254.169.254 immediately after inbound next-action POST
|
|
Long HTTPS sessions to mega.nz, transfer.sh, s3.amazonaws.com, *.blob.core.windows.net from non-developer endpoints
|
|
Sudden enumeration of ALL entries in AWS Secrets Manager / Azure Key Vault from a single ECS task identity
|
|
Process creation of rclone.exe, WinSCP.exe, fzsftp.exe, 7z.exe, tor.exe outside approved admin baseline
|
|
File-name patterns: *.snappy.parquet, *.tar.gz partition trees in /tmp/, /var/tmp/, C:\ProgramData\
|
Crystal Eye 5.5 Detection & Mitigation
-
Detection + Protection mode on WAN/DMZ; drop CVE-2025-55182 Flight-protocol SIDs; Tor exit-node/bridge drop rules; weekly SDN push from RP SOC
- Enable Antimalware File Scanner, Anti-phishing, AV, App Filter, Protocol Filter; quarantine suspicious .tar.gz & container images
- Retain 3-failure/168-hour ban; export Banned IP Logs to SIEM hourly; whitelist via change-control only
- Fingerprint crown-jewel Parquet/CSV/cred files; Reject mode on Internet-bound; Alert on east-west; ingest DLP reports into Threat Hunt Dashboard
- Enforce phishing-resistant MFA on every SSL VPN, WireGuard, RDP, admin UI; least-privilege micro-segmentation via Hosts & Groups and Advanced Firewall Zones
- Push 4 FulcrumSec domains, 2 Tox IDs, 3 email addresses into AAI blocklists; CTA feed for early IAB-credential-leak warning
Recommendations
The following operationally specific recommendations address FulcrumSec's confirmed attack chain:
- Patch / virtual-patch CVE-2025-55182 within 24 hours. This is FulcrumSec's confirmed primary entry point. Inventory every React Server Component / Next.js / Waku / React Router workload; enforce upgrade to React 19.0.1 / 19.1.2 / 19.2.1 or apply CE IPS virtual patch. CISA KEV deadline expired 26 Dec 2025.
- Universal credential & API-key rotation with mandatory expiry ≤90 days. FulcrumSec targeted unrotated 2021-vintage credentials at youX. Force-rotate every IAM key, Secrets Manager value, and Key Vault entry; enforce phishing-resistant MFA via CE 5.5 Entra ID SSO.
- De-privilege ECS / container task roles to least-privilege. The LexisNexis breach was catastrophic because one container role had read access to every Secrets Manager entry. Audit all task / pod / function roles and decompose into per-service roles.
- Deploy DLP MD5 fingerprinting on crown-jewel datasets. Pre-load Parquet partitions, MongoDB clusters, Redshift exports, and source repositories into CE DLP Sensitive File List; set Reject on outbound Internet-bound flows.
Worldwide Ransomware Victims
Ransomware activity this week shows a heavy geographic concentration, with the United States dominating at 49.74%, accounting for nearly half of all reported incidents. This reinforces its position as the primary target due to its large digital footprint and high-value organisations.
The second tier of impacted regions includes Australia (6.88%) and the United Kingdom (5.82%), followed by Germany (4.23%), and Canada and India (3.7% each). These countries continue to face consistent targeting, likely due to strong economies and widespread enterprise infrastructure.
A mid-range distribution is observed across Italy (2.65%), and multiple countries in the ~1–1.6% range, including Philippines, Taiwan, Indonesia, Spain, Malaysia, Argentina, Sweden, Brazil, Japan, Saudi Arabia, Mexico, and Colombia. This reflects broader global reach and opportunistic targeting by ransomware operators.
The long tail of affected countries, each contributing 0.53%, includes Turkey, Panama, Switzerland, Pakistan, Serbia, Egypt, Ghana, China, Morocco, Hungary, Peru, France, Bangladesh, Zambia, Kenya, and Sri Lanka. These regions experienced isolated incidents, indicating either targeted attacks or early-stage campaign spread.
Industry-wide Ransomware Impact
Ransomware activity this week shows a strong concentration in a few key industries, with Manufacturing leading at 21.16%, making it the most targeted sector. This aligns with its reliance on continuous operations and often outdated industrial systems, making it highly vulnerable.
The Retail sector (10.58%) and Healthcare (8.99%) follow, both representing high-value targets due to sensitive data and operational urgency. Business Services (7.94%) and IT (6.88%) also experienced significant activity, reflecting attackers’ focus on service providers and technology-driven organisations that can create downstream impact.
Other notable sectors include Construction (6.35%), and a cluster of industries at 3.7%, such as Media & Internet, Architecture, Hospitality, and Insurance, indicating steady but distributed targeting across service-oriented sectors.
Mid-to-lower tier activity is observed in Real Estate (3.17%), Federal and Law Firms (2.65%), and Consumer Services, Transportation, and Organisations (2.12%), suggesting opportunistic attacks rather than concentrated campaigns.
Minimal activity was recorded in Electronics (1.59%), Education and Minerals & Mining (1.06%), and Telecommunications (0.53%), reflecting either limited exposure or lower prioritisation by threat actors during this period.
