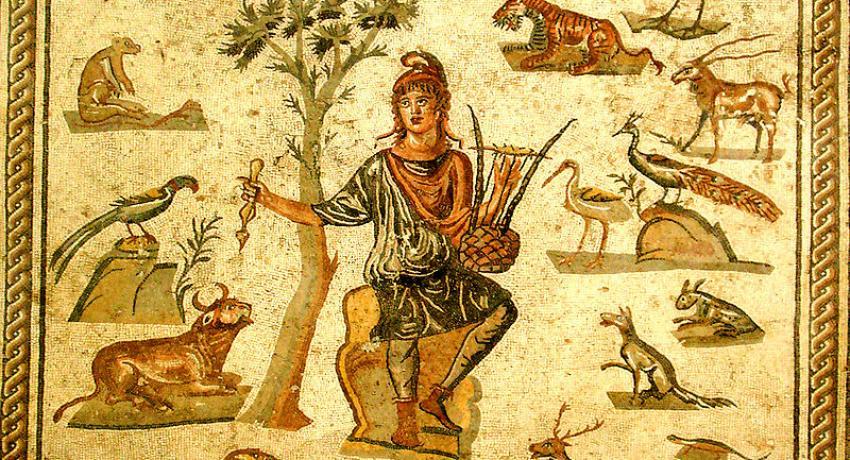
Orpheus surrounded by animals. Ancient Roman floor mosaic, from Palermo, now in the Museo archeologico regionale di Palermo. Picture by Giovanni Dall'Orto.
An age old authentication bypass vulnerability named ’Orpheus' Lyre’ dating back to the late 80’s has made it back to the headlines. The 20 years old vulnerability is said to have affected some of the implementations of the Kerberos protocol which is a cryptographic authentication protocol.
The Kerberos protocol basically facilitates secure communication over a network and uses tickets to perform this functionality. Kerberos had been named after the three headed mythological hound named Cerberus. Invented in the mid-80’s Kerberos protocols are widely used in websites which makes use of the Microsoft Active Directory.
The loophole or the flaw that allows attackers to bypass Kerberos has been named Orpheus’ Lyre due to its similarity with the Greek Mythological story of Orpheus. According to the story, Orpheus was able to sneak past the three-headed hound Cerberus after putting it to sleep by playing a tune with his lyre.
After its invention in the mid 80’s, the first production version of Kerberos called ‘Kerberos V4’ was first deployed at the Massachusetts Institute of Technology (MIT) in September, 1986. However, the Orpheus' Lyre vulnerability has not affected Kerberos V4, it has exposed loopholes in Kerberos V5. The vulnerability was found for the first time by security researchers Viktor Duchovni, Jeffrey Altman and Nico Williams for the first time in 1996 in the Heimdal implementation of Kerberos.
The Orpheus' Lyre flaw is related to the use of unauthenticated plaintext which can be exploited in a number of ways. The flaw can be used to steal credentials remotely and can also be effectively exploited to execute remote privilege escalation. However, researchers also point out to the fact that the Orpheus’ Lyre flaw can only be exploited by an attacker if only he/she is on-path between the client and the servers. So to be specific, the flaw can be exploited only through man-in-the middle attacks.
The authentication bypass vulnerability is said to exist in Microsoft Windows when Kerberos fails to prevent tampering with the SNAME field during ticket exchange (the vulnerability can be tracked as CVE-2017-8495). The same vulnerability is also prevalent in Heimdal, Samba, FreeBDS, and Debian which can be tracked as CVE-2017-11103.
The researchers who discovered this flaw have stated in their blog the vulnerability is detected on the clients-end and not in the server side. Henceforth, they advise to patch all affected clients since the servers cannot be patched to mitigate the Orpheus’ Lyre flaw.
Contact us for security vulnerability assessment.
