| New Threats Detection Added | • Katana Botnet • ACR Stealer |
| New Threat Protection | 147 |
| Newly Detected Threats | 14 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
Katana Botnet | |||||||||||||||||||||
|
Katana Botnet is a Maria malware variant that focuses on targeting Android TV set-top boxes. The android devices are being infected by ADB exploitation (Android Debug Bridge) and via residential proxy services. The Katana Botnet is only used for DDOS services and has not been identified to scan networks or steal credentials.
The Katana Botnet has been observed to kill any process running on Android that was not present on boot, likely to stop any other botnet malware from running on the same device. Katana also loads kernel modules to hide its presence and stop itself from being deleted; this has not been observed in similar android botnet malware. The Katana C2 controls and pushes new domains to the malware to assist in further persistence.
|
||||||||||||||||||||||
|
Threat Protected:
|
10 | |||||||||||||||||||||
|
Rule Set Type:
|
|
|||||||||||||||||||||
|
Class Type:
|
Domain-c2 | |||||||||||||||||||||
|
Kill Chain:
|
|
|||||||||||||||||||||
|
Threat name:
|
ACR Stealer | ||||||||||||||||||
|
ACR Stealer is an infostealer malware that is sold as part of a Malware-as-a-Service (MaaS) product. The infostealer has been around since 2023 and is compatible with a range of window operating versions. The stealer itself does not have any exclusive features that set it apart from other stealers. It’s written in C++, has C2 communication for execution and data exfiltration. It can steal data such as stored credentials, Web cookies, crypto wallets and configuration files.
|
|||||||||||||||||||
|
Threat Protected:
|
01 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Domain-c2 | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 3 - March 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-3rd-week-of-march-2026/647.
|
Vulnerability
|
CVSS
|
Description | Affected Version | Fixed Version | |
|
Craft CMS (CVE-2025-32432)
|
10
|
Unauthenticated RCE - Craft CMS contains a code injection vulnerability that can allow an unauthenticated remote attacker to execute arbitrary code on the system via a specially crafted HTTP request.
|
3.0.0-RC1 - 3.9.15
4.0.0-RC1 - 4.14.15
5.0.0-RC1 - 5.6.1
|
3.9.15
4.14.15
5.6.17
|
|
|
Laravel Livewire (CVE-2025-54068)
|
9.2
|
Unauthenticated RCE - Laravel Livewire contains a code injection vulnerability that can allow an unauthenticated remote attacker to execute arbitrary code on the system.
|
3.0.0-beta.1 - 3.6.3
|
3.6.4
|
|
|
Apple Multiple Products (CVE-2025-43510)
|
7.8
|
Sandbox Escape - Multiple Apple devices contain a memory management vulnerability that can allow a malicious application to modify memory that's shared between processes which can assist in a GPU sandbox escape. This vulnerability is known to be used within the DarkSword iOS exploit chain.
|
MacOS: 14.0 - 14.8.2, 15.0 - 15.7.2
tvOS, visionOS, watchOS, iOS, iPadOS, macOS: < 26.1
iOS, iPadOS: < 18.7.2
|
14.8.2, 15.7.2
26.1
18.7.2
|
|
|
Apple Multiple Products (CVE-2025-43520)
|
5.5
|
Privilege Escalation - Multiple Apple devices contain a buffer overflow vulnerability that can allow a malicious application to write to arbitrary kernel memory locations which can result in an escalation of privileges. This vulnerability is used within the DarkSword iOS exploit chain to elevate privileges for the execution of the final payload.
|
MacOS: 14.0 - 14.8.2, 15.0 - 15.7.2
tvOS, visionOS, watchOS, iOS, iPadOS, macOS: < 26.1
iOS, iPadOS: < 18.7.2
|
14.8.2, 15.7.2
26.1
18.7.2
|
|
|
Apple Multiple Products (CVE-2025-31277)
|
8.8
|
Remote Code Execution via WebKit - Multiple Apple Products contain a buffer overflow vulnerability within WebKit that can allow an unauthenticated attacker to execute code on the devices upon visiting a specially crafted web page. This vulnerability is used in the DarkSword iOS exploit chain.
|
Safari, iPadOS, iOS, tvOS: < 18.6
MacOS: 15.0 - 15.6
visionOS: < 2.6
watchOS: < 11.6
|
18.6
15.6
2.6
11.6
|
|
|
Cisco Secure Firewall Management Center (FMC) (CVE-2026-20131)
|
10
|
Unauthenticated RCE - Cisco Secure Firewall Management Centre (FMC) Software and Cisco Security Cloud Control (SSC) Firewall Management contain a deserialisation vulnerability that can allow an unauthenticated attacker to execute code on the device via an arbitrary HTTP request. Successful exploitation can result in the ability for an attacker to execute Java code with root privileges on the device.
|
6.4.0.13 - 7.0.8
7.1.0 - 7.2.10.2
7.3.0 - 7.4.5
7.6.0 - 7.6.4
7.7.0 - 7.7.11
10.0.0.0
|
7.0.9
7.2.11
7.4.6
7.6.5
7.7.12
10.0.1
|
|
|
Synacor Zimbra Collaboration Suite (ZCS) (CVE-2025-66376)
|
7.2
|
Cross-site Scripting - Synacor Zimbra Collaboration Suite (ZCS) contains a cross-site scripting vulnerability in the Classic UI that can allow an unauthenticated remote attacker to send an email containing malicious JavaScript which executes in a victim’s browser once opened.
|
10.0.0 - 10.0.18
10.1.0 - 10.1.13
|
10.0.18
10.1.13
|
|
|
Microsoft SharePoint (CVE-2026-20963)
|
8.8
|
Unauthenticated RCE - Microsoft SharePoint contains a deserialisation vulnerability that can allow an unauthenticated attacker to execute code on the system. This vulnerability affects Microsoft SharePoint Enterprise Server 2016, Microsoft SharePoint Server 2019, and Microsoft SharePoint Server Subscription Edition.
|
SharePoint Enterprise Server 2016: 16.0.0 - 16.0.5535.1001
SharePoint Server 2019: 16.0.0 - 16.0.10417.20083
SharePoint Server Subscription Edition: 16.0.0 - 16.0.19127.20442
|
16.0.5535.1001
16.0.10417.20083
16.0.19127.20442
|
|
|
Wing FTP Server Wing FTP Server (CVE-2025-47813)
|
4.3
|
Information Disclosure - Wing FTP Server contains an information disclosure vulnerability that can allow an unauthenticated remote attacker to disclose the full server path of the installation which may assist an attacker in further attacks against the system.
|
< 7.4.4
|
7.4.4
|
Updated Malware Signature (Week 3 - March 2026)
|
Threat
|
Description | |
|
XWorm
|
A Remote Access Trojan (RAT) and malware loader that's commonly used in cyberattacks to give attackers full remote control over a victim's system. It's part of a growing trend of commercialised malware sold or rented on dark web forums, often under the guise of a “legitimate tool.”
|
Ransomware Report |
|
|
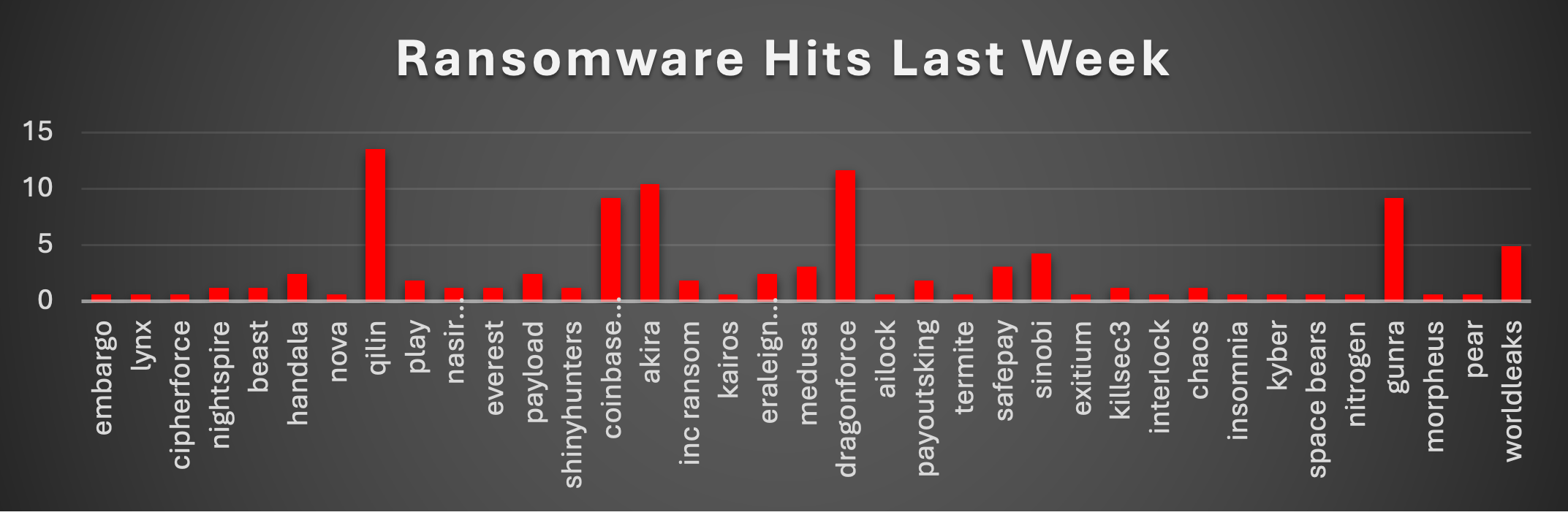
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity last week showed a clear shift in dominance, with Qilin leading the landscape at 13.5% of total attacks, making it the most active threat group. Close behind, DragonForce accounted for 11.66%, followed by Akira 10.43%, indicating a strong concentration of activity among a few top-tier operators. Notably, Coinbase Cartel and Gunra each contributed 9.2%, showing aggressive campaign activity and placing them firmly among the top ransomware actors for the week. WorldLeaks 4.91% and Sinobi 4.29% also demonstrated consistent operations, while groups like Medusa and SafePay 3.07% each maintained moderate presence. A mid-tier cluster of actors, including Handala, Payload, and Eraleign (APT73) 2.45% each indicates ongoing distributed activity beyond the primary players. Meanwhile, groups such as Play, INC Ransom, and PayoutsKing 1.84% continue to operate at lower but steady levels. At the lower end, a large number of ransomware groups, including NightSpire, Beast, Everest, ShinyHunters, KillSec3, Chaos, and others-contributed marginally ~1.23% or less each. This long tail highlights a fragmented ecosystem where many smaller or emerging groups are actively launching opportunistic attacks. |
Gunra Ransomware
Gunra is a Conti-derived Ransomware-as-a-Service (RaaS) operation first observed on April 1, 2025. The group employs double-extortion tactics, combining ChaCha20/Salsa20 file encryption with RSA-2048/4096 key wrapping and pre-encryption data exfiltration. Victims are given a 5-day deadline to initiate contact via a Tor-based negotiation portal styled after WhatsApp, with ransom demands ranging from $7M to $10M. Stolen data - often terabytes in volume - is published on the group’s dark web leak site (gunrabxbig445sjqa535uaymzerj6fp4nwc6ngc2xughf2pedjdhk4ad.onion) and the clearnet mirror datapub.news if payment is not received. As of March 2026, Gunra has claimed 20+ victims across manufacturing, healthcare, technology, financial services, education, and hospitality sectors spanning Brazil, South Korea, Japan, Canada, Egypt, Italy, UAE, Panama, Croatia, Colombia, Nicaragua, Australia, Thailand, and Hong Kong.
THREAT ACTOR DESCRIPTION
Group Profile
Gunra operates as a financially motivated RaaS syndicate that actively recruits affiliates on dark web forums. The group leverages leaked Conti source code to build high-speed, cross-platform encryption tools. Its ransom notes (R3ADM3.txt) and negotiation portals demonstrate professional operational tradecraft, including countdown timers, proof-of-decryption for sample files, and direct messaging channels via Proton Mail. Associated tools observed in breaches include Lumma Stealer (credential theft), DoNoT Loader (staging), and ConnectWise ScreenConnect (remote access).
Group Characteristics
|
Attribute
|
Details
|
|
Group Name
|
Gunra
|
|
First Observed
|
April 1, 2025
|
|
Operational Model
|
Ransomware-as-a-Service (RaaS) - affiliate-driven
|
|
Extortion Method
|
Double Extortion (Encryption + Data Leak)
|
|
Motivation
|
Financial
|
Malware Characteristics
|
Technical Attribute
|
Value
|
|
Programming Language
|
C/C++ (MSVC 2019/2022 on Windows; GCC 14.2.0 on Linux)
|
|
Target Platforms
|
Windows (Win32/Win64 PE) + Linux (ELF64 AMD64)
|
|
File Encryption
|
ChaCha20 stream cipher (Windows + Linux) / Salsa20 (earlier variants)
|
|
Key Protection
|
RSA-2048 / RSA-4096 asymmetric wrapping
|
|
File Extension
|
.ENCRT (appended to encrypted files)
|
|
Ransom Note
|
R3ADM3.txt (dropped in every directory)
|
|
Process Name
|
gunraransome.exe
|
|
Mutex
|
kjsidugiaadf99439
|
|
PDB Path
|
D:\wrk\tool\encrypter\x64\Debug\encrypter.pdb
|
|
Obfuscation
|
XOR + Base64 encoding; murmur2 hashing
|
|
Lineage
|
Conti ransomware (leaked source code, 2022)
|
|
Linux Variant Note
|
Weak RNG (rand()/time() seed) - partial key recovery possible (ASEC)
|
DETAILED TACTICS, TECHNIQUES & PROCEDURES
Initial Access
Gunra affiliates leverage multiple intrusion vectors through the RaaS model:
Credential Phishing: Spear-phishing campaigns using phishing kits that mimic legitimate portals. A spoofed Microsoft [email protected] sender has been observed. Phishing delivers initial stagers that download the Lumma Stealer for credential harvesting.
Exposed Remote Services: Exploitation of RDP, VPNs, and ConnectWise ScreenConnect instances using stolen credentials. A ConnectWise remote tool binary (MD5: c07b712a984a506042ea2cf6e193f20c, filename: Net-Admin-Supporto-Remoto-.ClientSetup.exe) was found in a confirmed breach.
Pre-positioning: Evidence of multi-day quiet access before encryption detonation, consistent with standard RaaS affiliate playbooks.
Execution & Lateral Movement
Defence Evasion
The malware employs multiple evasion techniques:
Command & Control
C2 infrastructure utilises:
Tor network for leak site operations and victim negotiation portals
Clearnet domain: datapub.news (hosted at 86.54.28.216 on BlackHost / AS174 Cogent)
Proton Mail channels for direct victim communication
Data Exfiltration
Impact
Final impact phase includes:
INDICATORS OF COMPROMISE (IOCs)
Malware File Hashes
SHA-256 Hashes
|
Hash
|
TI Platform Lookups
|
|
854e5f77f788bbbe6e224195e115c749172cd12302afca370d4f9e3d53d005fd
|
|
|
a82e496b7b5279cb6b93393ec167dd3f50aff1557366784b25f9e51cb23689d9
|
|
|
6d25d5c988a8cda3837dff5f294cbc25c97aea48dde1a74cba71a2439cab0a11
|
|
|
75e5621756e9d19efeac2bcbb2ac4711fb85243c03b0a19c05b18e31a780691e
|
|
|
25c8cb27947042de89d634b3e260e614e5b1425a89494fa4e4295bcabfa8ee48
|
|
|
6d59bb6a9874b9b03ce6ab998def5b93f68dadedccad9b14433840c2c5c3a34e
|
|
|
5530363373dfe8fa474c9394184d2c56a0682c6a178d6f1c3536a1a3796dff42
|
MD5 Hashes
|
Hash
|
Type
|
Description
|
TI Platform Lookups
|
|
9a7c0adedc4c68760e49274700218507
|
MD5
|
Primary Windows sample
|
|
|
94b68826818ffe8ceb88884d644ad4fc
|
MD5
|
Linux ELF variant
|
|
|
136e0bf4e5fe4d4249fe9570153a0b97
|
MD5
|
Windows variant
|
|
|
186c77101c027a465b14cb4a74f8381e
|
MD5
|
Windows variant
|
|
|
182024fc6c5fe0b1b33fdd9c7c37e368
|
MD5
|
Windows variant
|
|
|
7dd26568049fac1b87f676ecfaac9ba0
|
MD5
|
Windows variant
|
|
|
ae6f61c0fc092233abf666643d88d0f3
|
MD5
|
Windows variant
|
|
|
f6664f4e77b7bcc59772cd359fdf271c
|
MD5
|
Windows variant
|
|
|
4c0e74e9f94dff611226cd1619cb1e1d
|
MD5
|
Windows variant
|
Network Infrastructure
IP Address
|
IP Address
|
Role / Evidence
|
TI Platform Lookups
|
|
86.54.28.216
|
datapub.news
|
Tor Leak & Negotiation Sites
|
Onion Address
|
Purpose
|
|
gunrabxbig445sjqa535uaymzerj6fp4nwc6ngc2xughf2pedjdhk4ad.onion
|
Data Leak Site (DLS)
|
|
nsnhzysbntsqdwpys6mhml33muccsvterxewh5rkbmcab7bg2ttevjqd.onion
|
Negotiation / payment portal
|
|
2bw7r32r5eshwk2h7uekj3lwzorxds2jyhyzqyilphid3r27x5hsf4yd.onion
|
Chat server (victim comms)
|
|
jzbhtsuwysslrzi2n5is3gmzsyh6ayhm7jt3xowldhk7rej4dqqubxqd.onion
|
Updated client login portal
|
|
r3tkfu3h7sx4k6n7mr7ranuk5godwz7vlgvv2dk2fs2cbma5nailigad.onion
|
Updated backend server
|
Threat Actor Communication Channels
|
Platform
|
Identifier
|
|
Proton Mail
|
|
|
Proton Mail
|
|
|
Gmail
|
|
|
Phishing Sender (spoofed)
|
File & System Artifacts
|
Artifact Type
|
Value
|
|
Ransom Note Filename
|
R3ADM3.txt
|
|
File Extension
|
.ENCRT (appended to encrypted files)
|
|
Process Name
|
gunraransome.exe
|
|
Mutex
|
kjsidugiaadf99439
|
|
PDB Path
|
D:\wrk\tool\encrypter\x64\Debug\encrypter.pdb
|
|
Shadow Copy Deletion
|
vssadmin delete shadows /all /quiet
|
|
Keystore Pattern
|
{sha256_hash}.keystore
|
|
ConnectWise RAT Binary
|
Net-Admin-Supporto-Remoto-.ClientSetup.exe
|
|
ChaCha20 Magic Constant
|
expand 32-byte k
|
MITIGATION WITH CRYSTAL EYE 5.5
- IDPS (Inline mode, Security ruleset) - Deploy IDPS profiles in Inline mode on WAN-facing zones with the "Security" base ruleset.
- Gateway Antivirus - CE's gateway AV performs real-time signature + heuristic analysis on files in transit.
- Content Filter / Secure Web Gateway - Configure web filtering in Transparent with SSL Decryption mode to inspect HTTPS traffic to spoofed Microsoft portals. Block uncategorised and newly registered domains.
- CE's Forcefield application auto-bans IPs exceeding login attempt thresholds on the CE XDR management interface itself, preventing brute-force against the gateway.
IRAN-US-ISRAEL CYBER WAR - NEW IOCs (March 14-20, 2026)
Red Piranha identified the following IOCs during the last week of March 14-20, 2026.
Network Infrastructure
MuddyWater - New C2 Nodes
|
IP Address
|
Role / Evidence
|
TI Platform Lookups
|
|
206.71.149.51
|
MuddyWater command server (port 443)
|
|
|
143.198.5.41
|
Exfiltration endpoint (port 443)
|
|
|
209.74.87.67
|
Operation Olalampo C2 node
|
|
|
38.180.239.161
|
Sliver C2 on M247 Europe SRL - "Wonders Above"
|
|
|
104.238.191.185
|
Parasite SSH pivot (port 443)
|
Void Manticore / Handala - New VPS Infrastructure
|
IP Address
|
Role / Evidence
|
TI Platform Lookups
|
|
82.25.35.25
|
Handala VPS infrastructure
|
|
|
31.57.35.223
|
Handala VPS infrastructure
|
|
|
107.189.19.52
|
Handala VPS infrastructure
|
Malicious Domains
DOJ/FBI Seized Domains (March 19, 2026)
|
Domain
|
Actor
|
Purpose
|
Status
|
TI Platform Lookups
|
|
justicehomeland.org
|
Void Manticore / MOIS
|
Psyops - stolen data posting
|
SEIZED
|
|
|
handala-hack.to
|
Void Manticore / MOIS
|
Stryker attack claim / leak site
|
SEIZED
|
|
|
karmabelow80.org
|
Void Manticore / MOIS
|
Psyops - death threats
|
SEIZED
|
|
|
handala-redwanted.to
|
Void Manticore / MOIS
|
Posted PII of ~190 IDF personnel
|
SEIZED
|
Operation Olalampo C2 Domains
|
Domain
|
Actor
|
Notes
|
TI Platform Lookups
|
|
codefusiontech.org
|
MuddyWater
|
C2 - Python/Werkzeug backend
|
|
|
miniquest.org
|
MuddyWater
|
C2 server
|
|
|
promoverse.org
|
MuddyWater
|
C2 server
|
|
|
jerusalemsolutions.com
|
MuddyWater
|
C2 server
|
Staging Infrastructure
|
Domain
|
Actor
|
Notes
|
Status
|
TI Platform Lookups
|
|
meetingapp.site
|
Dust Specter
|
C2 domain
|
ACTIVE
|
|
|
line.completely.workers.dev
|
MuddyWater
|
Cloudflare Workers staging
|
ACTIVE
|
|
|
prism-west-candy.glitch.me
|
MuddyWater
|
Glitch-hosted staging
|
ACTIVE
|
|
|
datadrift.somee.com
|
MuddyWater
|
hosted staging
|
ACTIVE
|
Newly Observed Infrastructure
|
Domain
|
Actor
|
Source
|
TI Platform Lookups
|
|
justweb.click
|
Iranian APT cluster
|
Hunt.io (Mar 4)
|
|
|
girlsbags.shop
|
Iranian APT cluster
|
Hunt.io (Mar 4)
|
|
|
lecturegenieltd.pro
|
Iranian APT cluster
|
Hunt.io (Mar 4)
|
|
|
ntcx.pro
|
Iranian APT cluster
|
Hunt.io (Mar 4)
|
|
|
retseptik.info
|
Iranian APT cluster
|
Hunt.io (Mar 4)
|
RedAlert Phishing Campaign
|
Domain
|
Actor
|
Purpose
|
Status
|
TI Platform Lookups
|
|
shirideitch.com
|
Iran-linked
|
Malicious RedAlert APK host
|
ACTIVE
|
|
|
ra-backup.com
|
Iran-linked
|
C2 exfil (api subdomain)
|
ACTIVE
|
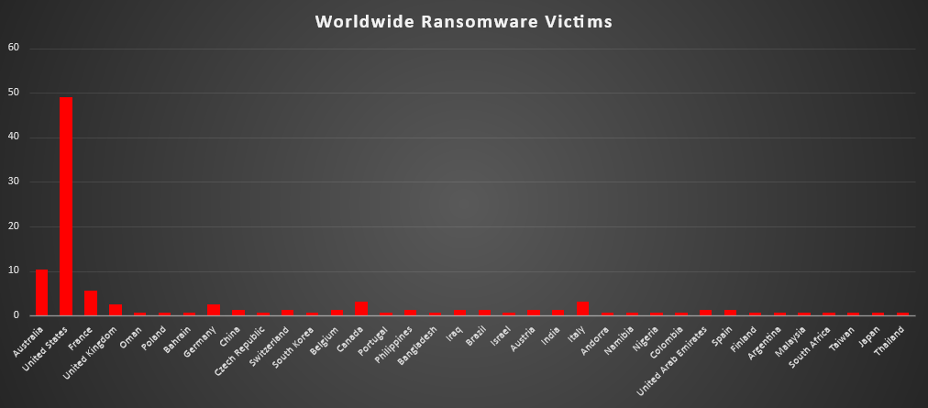
Ransomware Victims by Geography
A recent global analysis of ransomware victims highlights United States as the primary target, accounting for 49.08% of all reported incidents-nearly half of the global impact. This confirms that the U.S. continues to be the central focus for ransomware operators due to its high-value infrastructure and enterprise density.
The second most impacted country is Australia, contributing a notable 10.43%, showing a significant spike compared to typical trends. France follows with 5.52%, while Canada and Italy each account for 3.07%, indicating steady targeting across Western economies.
Countries like the United Kingdom and Germany reported 2.45% each, reflecting moderate but consistent ransomware activity. Meanwhile, a broader group, including China, Brazil, India, Spain, and the United Arab Emirates-each contributed around 1-1.23%, demonstrating the widespread global reach of ransomware campaigns.
A long tail of countries such as Japan, South Africa, Argentina, Malaysia, and others reported minimal shares ~0.61% each, indicating opportunistic or isolated attacks rather than sustained campaigns.
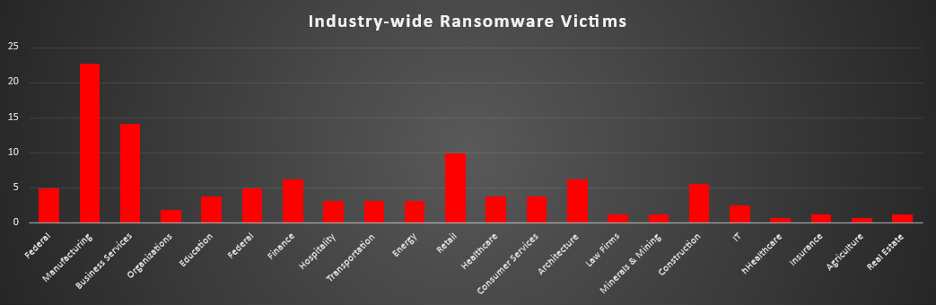
Industry-wide Ransomware Impact
Ransomware activity this week shows a strong concentration in a few key industries, with Manufacturing emerging as the most heavily targeted sector at 22.7% of all victims. This continues the trend of attackers focusing on operationally critical environments where downtime directly translates to financial loss, increasing the likelihood of ransom payment.
Business Services follows at 14.11%, reinforcing that service-based organisations-often connected to multiple clients-are high-value targets for broader impact. Retail 9.82% also saw significant activity, reflecting continued exploitation of customer-facing systems and transactional platforms.
Mid-tier sectors include Finance and Architecture 6.13% each, along with Construction 5.52% and Federal 4.91%, indicating steady targeting of industries that handle sensitive financial, structural, or governmental data. These sectors remain attractive due to both data value and potential regulatory pressure to recover quickly.
Other industries such as Education, Healthcare, and Consumer Services 3.68% each, along with Energy, Hospitality, and Transportation 3.07%, show consistent but moderate exposure. This suggests attackers are maintaining a diversified targeting approach rather than focusing exclusively on a single vertical.
Lower-impact sectors like IT (2.45%), Law Firms, Insurance, Minerals & Mining, Real Estate ~1-1.23%, and Agriculture 0.61% experienced minimal activity, likely due to either smaller attack surfaces or lower immediate financial returns.